Are you familiar with what an ICA file is and how to open .ica files?
The .ica file format is typically used to connect to remote desktops or applications. When a user opens an ICA file, the Citrix Receiver client software connects to the remote server using the data in the file and starts the desired application. Formats like JSON file & ICA are pretty important in today’s digital age of information.
Accessing remote desktops and applications is simple with this format. They offer a secure connection and are simple to use. In this article, we will cover what ICA files are, how to open them, and their advantages.
What is an ICA File?

An ICA (Independent Computing Architecture) file serves as a specific file format used by Citrix systems. It is commonly linked with Citrix XenApp and XenDesktop, both being remote solutions that enable users to reach applications or desktop environments operating on a distant server.
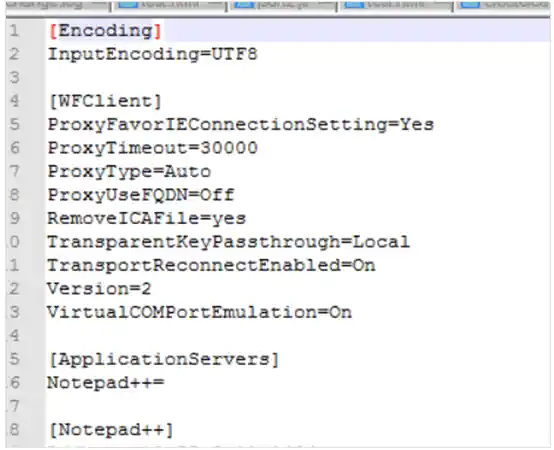
Within the ICA file, there exist configuration details and directives. These include the server’s location, port identification, authentication credentials, and various configurations meant for the Citrix Receiver. The Citrix Receiver is software that is installed on the user’s device. After the user initiates these files, the Citrix Receiver analyzes them and establishes a link to the remote server. This established connection then allows the user to effectively engage with the applications or desktops that are hosted on that specific server.
Businesses of considerable scale adopt the usage of ICA files and Citrix clients to extend remote accessibility to vital business applications for their employees. This approach also offers the advantage of creating a standardized procedure for deploying and accessing applications.
Benefits of Using .ica File
- Remote access: They enable individuals to connect with computer desktops and software situated remotely. This kind of setup can be advantageous for enterprises aiming to empower their staff to work away from the office or while traveling.
- Data Protection: The aforementioned ICA files use encoding techniques to safeguard information transmitted between the user’s personal computer and the distant server. This measure is taken to ensure that unauthorized entry to the information is prevented.
- Flexibility.ICA files possess the ability to establish links with a diverse range of software applications. This attribute grants them adaptability, rendering them a multi-faceted instrument suited for a broad assortment of scenarios.
- User-Friendly: The process of utilizing these files isn’t excessively complex. Following the creation of one such file, individuals can initiate a connection to the distant software or desktop with a mere double-click.
- Cost Reduction in IT: ICA files can potentially curb IT-related expenditures. This is achieved through the elimination of the necessity to acquire and sustain physical servers and workstation units.
- Enhanced Operational Speed: The implementation of ICA files can potentially result in operational swiftness by moving the application processing workload to the remote server.
Image Object Content Architecture File Format
An ICA file can also be saved in the Image Object Content Architecture (IOCA) format. It uses a pixel pattern picture composed of numerous sections. Each section holds picture information, in addition to particulars outlining the picture’s attributes.
The Image Object Content Architecture layout was formulated by IBM. This configuration, self-sufficient from platforms, is applied to swap visual information. Every IOCA configuration document embodies an account of itself and its content, sanctioning software to scan and handle the document without supplementary data.
IOCA visuals are typically safeguarded under ICA records. These records include single or multiple visuals, presented across one or multiple pages. The visuals could be compacted and can range from monochrome to grayscale to multicolored. Predominantly, ICA documents find usage in the reproduction and safeguarding of visuals.
How to Open ICA Files?
To access an ICA (Independent Computing Architecture) file, it’s necessary to have the Citrix Receiver or Citrix Workspace installed on your device. To get these applications and open the file using them, follow these steps:
- Visit the official website for Citrix (https://www.citrix.com) through a web browser.
- Click on the “Download” option.
- Search for the client software, either Citrix Receiver or Citrix Workspace. The available versions or editions of the client software might vary based on the website design and current Citrix offerings. Select the version that matches your operating system.
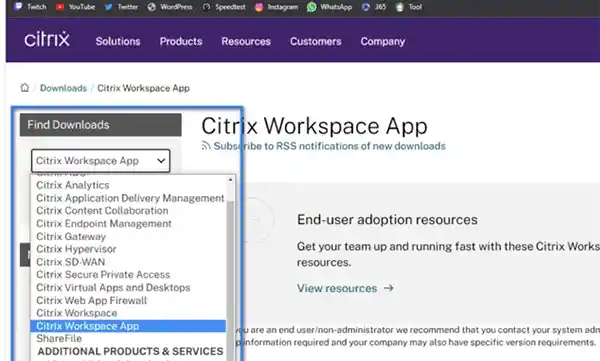
- Select the download link given for the preferred client software.
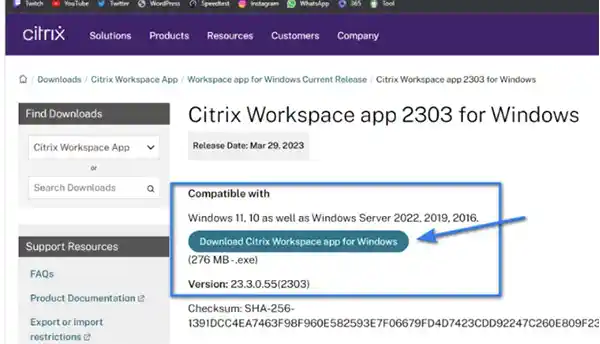
- After the installer file is acquired, locate it on your computer and initiate the installation by performing a double-click.
- Adhere to the instructions on the screen that the installer presents. This usually involves accepting the terms of the licence agreement, determining the installation location, and picking any added components or preferences you’d like to include.
- After the installation concludes, the Citrix Receiver or Citrix Workspace client software should be set up for use.
- Locate the particular ICA file that you intend to open.
- Right-click on the file, then opt for “Open with” followed by selecting “Citrix Connection Manager” from the list of provided programs.

- The suitable application will launch and begin the connection process to the remote server indicated in the ICA file.
- If requested, input your credentials, like your username and password, to confirm your identity with the remote server.

- Once the connection is successfully established, the virtualized application or desktop mentioned in the ICA file will be visible on your screen. You can interact with it as though it’s functioning locally on your device.

Similar to VTT Files and the BKUP File format, you also have the option to open an ICA file through a text editor, like Notepad or Notepad++. Nonetheless, this approach will only permit you to examine the textual material within the file, rather than accessing the genuine configuration details.
How to Create .ica Files?
ICA files can be generated through a range of methods, such as employing the Citrix Receiver client, a text editing program, or third-party software.
For initiating the creation of an ICA file via the Citrix Receiver client, adhere to these guidelines:
- Open the Citrix Receiver client.

- Access the Tools section and opt for ICA File Generation.
- Within the ICA File Generation interface, input the ensuing particulars:
– Server Address: The IP address or domain name of the distant server.
– Port Number: The designated port number of the distant server.
– Username: Your respective username for remote server login.
– Password: The authentication key for remote server entry.
– Application Name: The title of the preferred application for connection.
- Execute the Creation command.
By following these steps, the Citrix Receiver client will compile an ICA file, preserving it in your specified directory
How to Convert an ICA file?
You have the option to use any of the third-party tools to convert .ICA files.
- Simply choose the “Select File” button associated with your .ica file on the webpage.
- Once your file is accessible within the browser, proceed to the “Save as…” function within the menu.
- From there, pick your preferred image format (such as JPG, PNG, TIFF, PDF, and so forth).
- The conversion process will be initiated, followed by the download of your transformed file.
Here are some third-party software solutions capable of accessing and converting ICA files:
- Identity Compass (encrypted responses): Identity Compass functions as an employee selection tool, using a collection of “thinking structures and preferences” to record individuals’ cognitive processes and decision-making in regular occupational scenarios, thus anticipating potential employee success. Encrypted answers from this software’s queries are archived in ICA files. This file type is categorized as Encoded.

- XnView (bitmap images): XnView serves as a universal image browser, editor, and converter, spanning across various platforms. It also features tools for batch image manipulation and resizing. ICA files containing image data can be opened using this application.

How to Troubleshoot ICA File Citrix Problems?
Here are some steps to consider if you’re encountering difficulties with ICA files in Citrix:
- Verify the ICA File’s Validity: Open the file using a text editor to confirm that it contains accurate information.
- Verify the Server Location and Port: Make sure that the server location and port information provided in the ICA file are correct.
- Review Authentication Details: If a username and password are required for connecting, ensure that accurate login credentials are being used.
- Validate Citrix Receiver Configuration: It’s essential that the setup and configuration of the Citrix Receiver client are accurate in dealing with ICA files. Confirm its proper arrangement on your device.
- Restart Citrix Receiver: Sometimes, restarting the Citrix Receiver client can troubleshoot problems with the files.
- Seek IT Administrator Assistance: If none of the above steps resolves the issue, reach out to your IT administrator for further guidance.
Suggest read: What is LightingService.exe? Explained
Conclusion
In conclusion, an ICA file stands as a configuration file applied by Citrix application servers. It embodies details concerning the link between an individual’s computer and the distant server.
ICA files extend a range of advantages, covering distant reach, safety assurance, adaptability, and user-friendliness. These files present a practical and safeguarded approach to approach remote desktops and applications. If the necessity to approach a remote desktop arises, using an ICA file proves to be a worthwhile choice.
Read Next: How to Format an SSD for Windows and Mac: The Ultimate Guide
Frequently Asked Questions (FAQs)
A: The full form of the ICA file is “Independent Computing Architecture” file.
A: It is a textual file arranged using XML. The XML document holds the setup details for the ICA file, like the server location, the designated port digits, the user validation particulars, and the desired application for user linkage.
A: The possible configurations in an ICA file differ in line with the version of the protocol. Yet, a few shared configurations involve the server location, the port identification, the user validation data, and the title of the application.
Sources:

